228 private links
lol
This talk will investigate how the concept of private property has fundamentally altered our behavior towards the environment. We will investigate how an alternative ontology of electronic waste is needed and argue why dumpster diving, hacking and reverse engineering abandoned electronics is more relevant than ever to tackle this problem.
Within the discourse that surrounds the global rise in electronic waste, only a select range of subjects receive attention from the public - international relations, global waste management strategies and corporate greenwashing rhetoric that emphasizes a ‘circular’ economy. Although the legitimacy of these strategies can be debated, they fail to address the root of the problem. Following the pervasive concept of private property and how it has infiltrated the ways in which we think about ourselves, our relationships between each other and the environment, we will arrive at how this concept has solidified itself within the ontological frameworks we use to make sense of waste and electronic waste in particular. We will discuss how, when we get rid of the concept of private property (and subsequently the concept of waste), we can reimagine what abandoned electronics mean to us and how we can best address the incessant pressure from manufacturers to treat them as expendable, throw-away objects. We will discuss how collective dumpster diving, hacking and reverse engineering abandoned electronics might be a possible solution and present free and open source tools that could aid us in the process.
Betula is a free federated self-hosted single-user bookmarking software for the independent web. Use it to organize references or maintain a linklog.
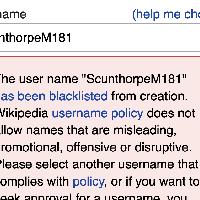
The Scunthorpe problem is the unintentional blocking of online content by a spam filter or search engine because their text contains a string (or substring) of letters that appear to have an obscene or otherwise unacceptable meaning. Names, abbreviations, and technical terms are most often cited as being affected by the issue.
QWERTY keyboard is widely used for information processing nowadays
in Japan, United States, and other countries. And the most frequently asked
question about the keyboard is: “Why are the letters of the keyboard arranged
the way they are?” Several papers in the field of information processing answer
the question like this: “To slow down the operator.” It’s nonsense.
In this paper we reveal the prehistory of QWERTY keyboard along the his-
tory of telegraph apparatus: Morse, Hughes-Phelps, and Teletype. The early
keyboard of Type-Writer was derived from Hughes-Phelps Printing Telegraph,
and it was developed for Morse receivers. The keyboard arrangement very
often changed during the development, and accidentally grew into QWERTY
among the different requirements. QWERTY was adopted by Teletype in the
1910’s, and Teletype was widely used as a computer terminal later.
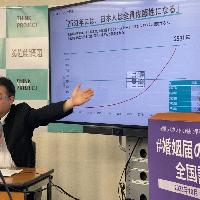
"Yoshida determined that by 2531, only 7.96% would be named Sato under the selective separate surname system, but the Sato surname would still take over by the year 3310.
At the same time, if Japan's population decline continues at the current speed, there will be only 22 people left in 3310."
Free culture licensing is its own special bugbear. While pioneers like the GPL, ISC, and even WTFPL have served their purpose, with the advent of source-available but non-libre licenses and ensnaring of public works by corporate interests, it's time we take a new tack.
To that end, I propose that new projects choose a license from what I call the "Poison Pill" class. These are licenses that are so nonsensical that any entity with an actual legal department won't use them out of terror; however, normal, every day people have no such strict adherence to legalese and can enjoy them as the art they are in themselves. Below, I've included 40 such licenses with easy-to-use template variables so you can adapt them to your project:
3D DOM viewer, copy-paste this into your console to visualise the DOM topographically.
The repression that environmental activists who use peaceful civil disobedience are currently facing in Europe is a major threat to democracy and human rights. The environmental emergency that we are collectively facing, and that scientists have been documenting for decades, cannot be addressed if those raising the alarm and demanding action are criminalized for it. The only legitimate response to peaceful environmental activism and civil disobedience at this point is that the authorities, the media, and the public realize how essential it is for us all to listen to what environmental defenders have to say.
Envisioning a Neuromancer game developed for the revolutionary new Commodore Amiga by his own company Futique, the fabulously well-connected Leary assembled a typically star-studded cast of characters to help him make it. It included David Byrne, lead singer of the rock band Talking Heads; Keith Haring, a trendy up-and-coming visual artist; Helmut Newton, a world-famous fashion photographer; Devo, the New Wave rock group; and none other than William Gibson’s personal literary hero William S. Burroughs to adapt the work to the computer.
I recently posted the table of contents and a chronological list of network entries that will appear in Other Networks: A Radical Technology Sourcebook. As I try to make clear in the introduction, most entries also include examples of experiments with or on these networks because we often don’t know just how compelling a given network can be until we see artists exploring its limits and possibilities. Not surprisingly, however, just as we rarely understand how networks actually work, from the moment we send to the moment we receive, we also rarely attend to the underlying workings of media art. Stories abound of how, for example, artists from the 1970s and 1980s plugged this into that which resulted in certain fascinating outputs; but details are often frustratingly lacking or altogether absent on how the connections took place, even when the ‘how’ is exactly the point. To that end, I have also tried to include network diagrams and technical details for these experiments wherever possible.
document and experiment with networks outside of what’s now called “the internet.” We are invested in digging up alternative and forgotten networks so that we can reimagine the future of the internet as the future of networks.
plugdata is a free/open-source visual programming environment based on pure-data. It is available for a wide range of operating systems, and can be used both as a standalone app, or as a VST3, LV2, CLAP or AU plugin.
diagram.website: an incomplete map to regions of the handmade, personal, indie internet
Having created time-based, moving graphics jewels since 1975, utilizing LCD technology, I set as my next goal to create truly cybernetic jewelry. This meant a significant portion of the esthetic entity comprising the jewel would reside in a software program, executing in real time on a microcumputer residing in the jewel and contolling an output device—in this case an LCD panel with custom graphics. The patterns in this LCD would move and change under software control. Importantly, this meant that competely different looks could be obtained without changing the hardware in any way, something never before possible. Additionally the software could make decisions about how to control its output, based on internal and external monitoring of its environment, adding a component of "intelligence" not to be found without using computers. For the first time ever, jewelry objects could be endowed with simple, but real, aspects of awareness and volition- the first seeds of AI jewlery.